Introduction In a landscape where cyber threats evolve at breakneck speed, the adage “prevention is better than cure” has never been more apt. For businesses, particularly those operating on a global scale, the importance of preemptive security measures cannot be overstated. Delaying action until after an incident occurs is akin to locking the barn afterContinue reading “Shield Your Data: The SASE Roadmap to Cloud Security Success”
Tag Archives: cloud security
Safeguarding Your Assets: Essential Strategies for Multi-Tenant Cloud Security
Introduction In today’s digital age, cloud computing has emerged as a transformative force, offering businesses unparalleled opportunities to streamline operations, reduce costs, and drive innovation. By leveraging on-demand services over the internet, organizations can access a wide range of resources—from infrastructure and software to platforms without the need for extensive upfront investments in hardware orContinue reading “Safeguarding Your Assets: Essential Strategies for Multi-Tenant Cloud Security”
The Pillars of Cloud Security: Safeguarding Your Digital Assets
In an increasingly digital world, cloud security has become paramount for individuals and businesses. The pillars of cloud security form the foundation for protecting sensitive data, applications, and infrastructure in the cloud. This article aims to explore the key pillars of cloud security and how they work together to safeguard your valuable digital assets. HowContinue reading “The Pillars of Cloud Security: Safeguarding Your Digital Assets”
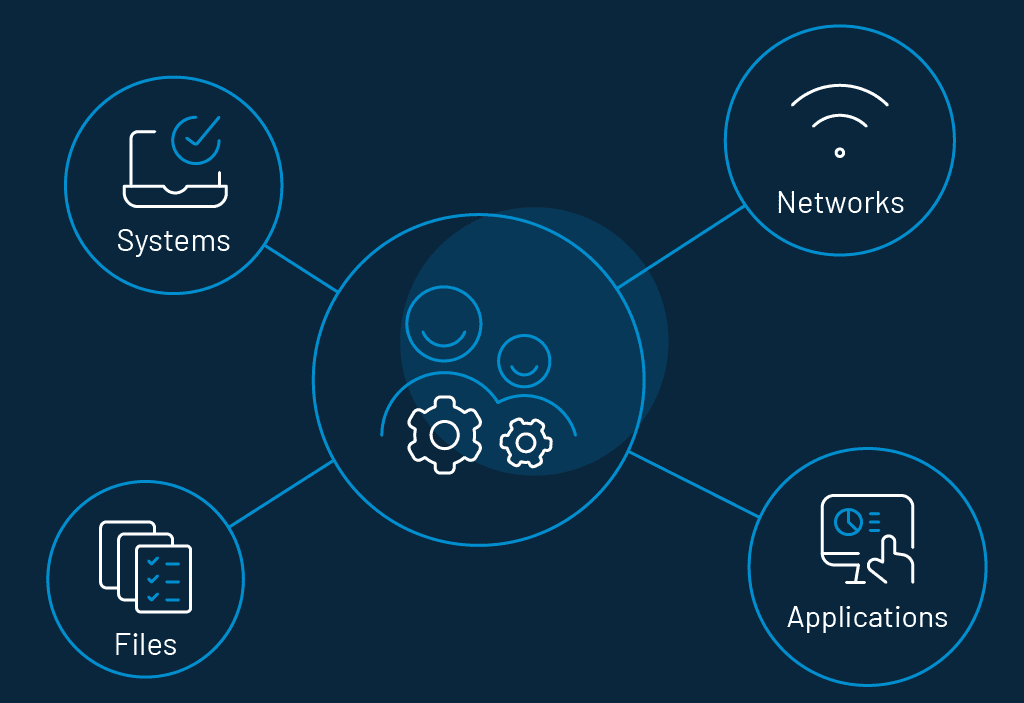
How Cloud IAM Protect Identities in the Enterprise Architecture
Identity management in cloud computing is primarily concerned with dealing with personal identity information in order to accurately control a user’s access to data, computer resources, applications, and services. A few years ago, business leaders, particularly key decision-makers, were focused on establishing an innovative IT environment that delivered operational agility and competitive advantage as crucialContinue reading “How Cloud IAM Protect Identities in the Enterprise Architecture”